From MIT Math Major to Encryptor of Elections
-
-
Slice of MIT
Filed Under

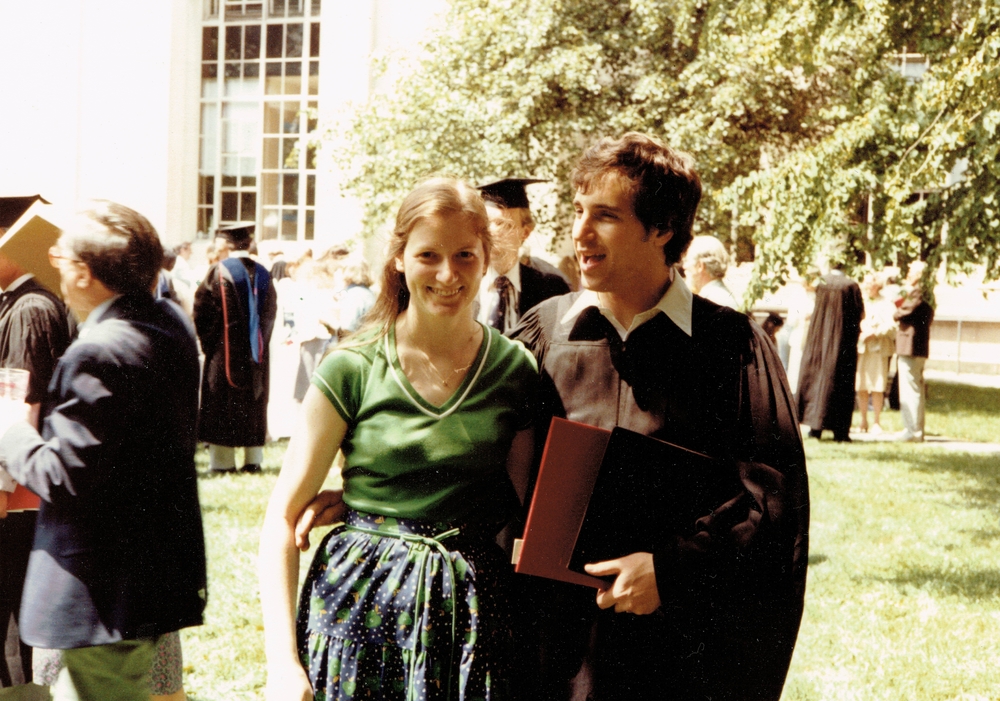
The United States recently weathered perhaps its most fraught presidential election in living memory, with an electorate riven not only by a global pandemic but also social upheaval and severe political division. Added to all this were widespread concerns about election security and legitimacy, which weren’t helped by the echoes of proven foreign meddling in social media during the 2016 election season and an incumbent president who refused to accept 2020’s election results. Yet with all that, the system worked, says Josh Benaloh ’81.
Benaloh, whose MIT degree is in mathematics, has a professional opinion on the topic. He works on ensuring election integrity as a senior cryptographer and computer scientist for Microsoft. “As far as the actual security of the election, in terms of casting and counting of votes, that seems like it was about as good as we’ve seen in recent years. Things seemed to go pretty well,” he says. “The flip side is that confidence in the integrity of elections is way, way down. All of a sudden we have millions of people who don’t trust their local election officials.”
Even without the charged political climate of recent years, such concerns are easily understood, notes Benaloh: “In other endeavors in life and society, people have an opportunity to check and see for themselves that what they’ve done has happened the way they wanted it to. They buy something, they can see that it matches what they asked for. They can check their bank accounts. But with voting, typically you can’t.”
The problems extend beyond the concerns of individual voters. “The US election infrastructure is a strange thing,” says Benaloh. “There is really no such thing as ‘a presidential election’ in the US. What we have instead are roughly eight to nine thousand simultaneous elections administered by local election officials.” Each of those separate elections offers individual possibilities for tampering with the process—especially in light of new technologies that didn’t exist when the Founding Fathers wrote the Electoral College into the Constitution.
Protecting against these and other vulnerabilities has been Benaloh’s professional mission for more than 30 years. Benaloh and Microsoft are now working to ensure election security through software named, appropriately enough, ElectionGuard.
Part of a larger Microsoft program called Defending Democracy, ElectionGuard is based on sophisticated cryptographic techniques designed to circumvent the particular qualities that can put US elections at risk—qualities that some cite as advantageous. For example, Benaloh says, “People often cite the diversity of the US electoral system as a security benefit. They’re completely wrong about that. It actually makes it more vulnerable.”
Securing digital systems such as your computer or internet connection is generally based on a time-honored military doctrine called “defense in depth”—forcing an attacker to break through multiple layers before reaching the vulnerable center. But the broadly heterogeneous and decentralized nature of the American electoral system makes this practically impossible. “By having this heterogeneity, we effectively give attackers a menu of options and they can attack the weakest links,” Benaloh explains.
Benaloh believes that the decentralized nature of the US electoral process poses another complication: “Most election jurisdictions are small local governments that are worrying about potholes and other issues along with elections,” he says. “And they have part-time staff or county auditors who might not be security experts. The infrastructure we have is not something that one would choose to design if you wanted high integrity in elections.”
I took a freshman seminar that gave an overview to some new methods of modern cryptography, things just being published at the time. It was all a new field, with green grass and lots of places to explore and find new things.
Cryptography in action
To meet these challenges, Benaloh says, ElectionGuard was designed as an add-on to the country’s wide range of existing voting systems. “This is a secondary system that’s closely integrated,” he says. It relies on a cryptographic technique called homomorphic encryption. With traditional encryption, Benaloh explains, encrypted data might be stored or transmitted to someone else, but nothing else can be done with it until it’s eventually decrypted. In contrast, homomorphic encryption allows computations to be performed on the data while it is still in encrypted form.
“In the elections, the only computation that’s really being done is adding up votes—simple addition,” Benaloh says. “We can combine the encrypted ballots into what is effectively one ballot that has all of the sums. Individual votes never have to be decrypted. They can just be combined in encrypted form, and only this aggregate tally needs to be decrypted.” In this way, ballots are kept inviolably confidential—and thus protected from tampering—from the time voters cast their choices to the time they’re counted.
The software provides another major benefit that could build public confidence in elections: verifiability. With ElectionGuard, “Voters are no longer just dropping a vote at the ballot box and going home and crossing their fingers,” he says. Voters would have tracking codes to look up their encrypted ballots and confirm that they were correctly counted. When the ElectionGuard software had its first full-scale test run in February 2020 during a primary election in the small farming town of Fulton, Wisconsin, it passed with flying colors: The results as reported by ElectionGuard precisely matched those obtained by old-fashioned hand counting.
It’s a great beginning for ElectionGuard, but there’s more to be done. The Covid-19 pandemic interrupted plans for several more trials. Among officials scrambling to make elections happen in this climate, Benaloh says, “There’s not a lot of stomach right now for trying new things.”
As the dust settled from November 2020, however, ElectionGuard did have the opportunity to spread its wings a bit. Benaloh explains, “We participated in a post-election audit in Inyo County, California, that used this technology in a somewhat different way”—preserving privacy while the integrity of the election was verified. Another test came in the US Congress. “The House Democratic Caucus used this technology for its leadership vote right after the November election—for the speaker and the majority leader, the majority whip, positions like that. It’s typically done in person with a traditional ballot box, but they wanted to be able to do things remotely because of the pandemic and other issues. And we were able to use the ElectionGuard technology to provide an end-to-end verifiable election.”
Benaloh admits that this was something of a special case. “We do not advocate broad use of this technology for internet voting, but this was a very limited, very controlled environment. Every single member of the House of Representatives is issued a smartphone that’s centrally administered. And we were able to use that infrastructure to have direct video communications with the members during the election. So a lot of the issues that would be a concern in internet voting really didn’t apply in this case.”
By all accounts, the congressional test was a rousing success. “They seemed very happy with it,” says Benaloh. “It shows the flexibility of this technology, that in about a month or so it could be purposed to this very different application from what we were considering. It’s a proof of the effectiveness and the flexibility that we were able to create.”
Finding the “green grass” at MIT
Benaloh had always expected to be a mathematician, but it was during his undergraduate years at MIT that he first encountered the possibility of an alternate path. “One thing that I’m very glad of is that, as an undergraduate, I was perhaps a little bit bolder and more unfettered than I should have been, so I wasn’t afraid to take graduate classes when I thought they looked interesting,” he observes. “I took a freshman seminar that gave an overview to some new methods of modern cryptography, things just being published at the time. It was all a new field, with green grass and lots of places to explore and find new things.” In it, he saw “a nice mixture between my mathematics and computer science and a good way to straddle the boundary and find interesting work.”
In his senior year, he took a graduate class with Ronald Rivest, one of the fathers of modern cryptography. “I took his class in the spring of 1981, immediately after the 1980 election, so I wondered a little bit about whether cryptography could be applied to elections in interesting ways.” That became his final class project. Later, after graduate work at the University of Chicago and a move to Yale to concentrate on computer science, he developed his ideas further in his 1987 doctoral dissertation, Verifiable Secret-Ballot Elections, which introduced the idea of applying homomorphic encryption to elections.
“At that point, there had been more work done on cryptography and more tools available. I was more experienced and I was able to take these tools and build significant things out of them,” he recalls.
While the unusual upheavals of this past election year have brought quite a lot of attention to the things he has built—including in-depth articles in the New Yorker and Wired—Benaloh looks forward to a calmer period. But the work continues. Benaloh and Microsoft are planning further pilot testing runs, forging new vendor partnerships, and tweaking the ElectionGuard code to add new capabilities and increase compatibility with open-source software. With 2022 midterm elections on the not-too-distant horizon, “we’re in it for the long haul,” he says. “We have high hopes for coming years.”
Are you celebrating a milestone anniversary of your MIT graduation like Josh Benaloh and the Class of 1981? MIT Tech Reunions will take place as a multiday online event June 4–6, featuring special online events for reunion-year classes.
Not celebrating a reunion this year? The entire MIT community can learn from faculty during Technology Day, watch the online Tech Night at Pops, and explore sessions that highlight the MIT campus, programs, and departments. Learn more about how you can participate in Tech Reunions.
Illustration: Emily Muldoon Kathan/MIT Alumni Association
Mark Wolverton is a 2016–17 MIT Knight Science Journalism Fellow.









